Vidalia, Louisiana is a small city of around 4,000 residents, known for it’s beautiful riverfront. Though small, a hydroelectric plant allows Vidalia to provide residents with robust services and a great quality of life.
Andrew Jones, an IT technician, along with two others manage the information technology needs of the city, including City Hall, the Police Department, Fire Department, Utility Department, Parks and Recreation Department, and more.
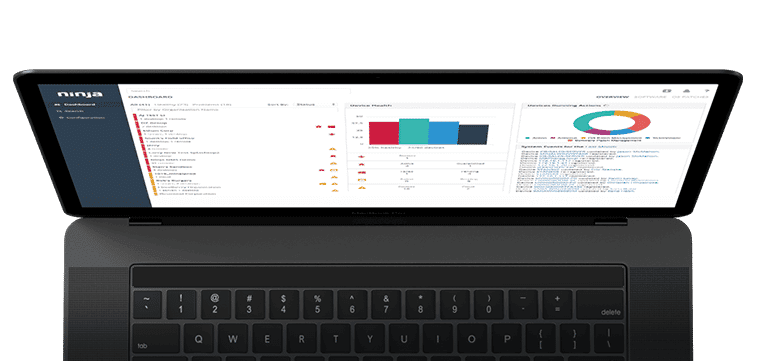
In 2019, Vidalia was subject to a ransomware attack due to poor vendor practices, and they decided to take back control of their IT infrastructure. As part of that effort, Vidalia purchased NinjaOne to provide visibility, control, and security across their systems.
Leveraging technology to keep the IT team lean
With only three full time technicians, the City of Vidalia has a lean IT operation. Even so, the departments those technicians service expect results. By using Ninja, the IT team is able to streamline some of the most time-intensive tasks they had previously performed manually.
“Ninja’s automated patch management feature has very beneficial for us,” says Andrew, “We’re running scans and installing updates daily, and automating weekly reboots on workstations every weekend away from peak hours. We still manually reboot servers so we can minimize downtime, but otherwise patching is fully automated.” Andrew’s team also uses Ninja’s third party application patching solution to roll out software like Libre Office, Chrome, and Adobe and to automate patching for this software. Prior to Ninja, the City of Vidalia had an employee that dedicated 20 – 30 hours per week to traveling between locations and updating endpoints manually, as well as manually running Anti-Virus scans. They’ve been able to shift almost an entire employee salary from scanning and patching to other critical IT tasks.
Twice per year, the IT team would also perform an IT asset audit. They would go to each of their managed agencies and take a full hardware inventory and use that inventory for asset planning. “With Ninja, our IT asset inventory is fully automated and updated live. This makes a huge difference because now when we go to do hardware upgrades, we’re looking at real-time device configurations, not what our assets were six months ago,” explains Andrew. Ninja’s live IT asset inventory not only saves IT team time, it saves the city money.
Building a more proactive support organization
Andrew’s team uses Ninja to automate ticket creation for critical conditions. “We use the Ninja NMS agent on our network devices, IOT devices, and printers. When Ninja detects a series of failed pings, we get both an alert in Ninja and a ticket created in our helpdesk so we can solve the issue before end-users really even notice,” says Andrew, “We’re also automatically generating tickets when specific services crash, when SMART status is degraded, for RAID issues, and more.”
“We’re also leveraging the Ninja custom system tray icon to make submitting a ticket easier, says Andrew.” The Ninja system tray icon is visible to all endpoints with a Ninja agent installed so that users can easily submit a ticket to the IT department. The City of Vidalia also includes critical links to resources like security awareness training on the system tray icon to make those resources more readily available to users.
Achieving compliance
“Compliance is very important for the agencies we manage, from CJIS compliance for our Police Department to PCI compliance for City Hall. Automating patch management through Ninja allows us to keep our operating systems up-to-date, making both achieving compliance and reporting on compliance far easier,” says Andrew.
Drive encryption is also important to meet compliance requirements across agencies. The City of Vidalia uses Ninja to ensure that drives are encrypted and automatically collect BitLocker encryption keys in case a drive needs to be recovered.
“Like many municipalities, our cyber insurance company requires us to enforce multifactor authentication across the tools we use,” says Andrew. Ninja enforces multifactor authentication not just for user login, but also when technicians take actions that could have significant security implications, such as creating new users, modifying scripts, or accessing credentials.
“We actually had to remove Ninja’s Splashtop remote control tool from our Police Department endpoints for a while,” says Andrew. Before Ninja implemented ‘ask permissions’ for Splashtop there were both compliance challenges and concern from departmental leadership about the access IT had to endpoints. “After Ninja updated Splashtop so that end-users can reject remote access, we added it back on all of our endpoints,” says Andrew. Ninja now automatically generates a remote access report and emails it to their CISA every month so there is a record of all remote connections. “We really like the fact that user history and actions are recorded and can be reported on. It gives some of the department director heads comfort knowing that we only remote in whenever there’s an issue, and questions can be asked if there are any doubts. Accountability for a user’s actions within a position of power is important,” says Andrew.
Building a more secure network
In addition to using Ninja’s to automate patching, Andrew and his team rely on Ninja to address unexpected security vulnerabilities. “When the Print Nightmare vulnerability was discovered, I logged into Ninja and stopped and disabled the print spooler service on our servers without even remoting into them,” says Andrew. “When there was a ransomware outbreak wreaking havoc across the country about a year ago, I used the scripting feature to disable SMBv1 across all of our devices. When there was a vulnerability with the Dell SupportAssist software, we used Ninja to create a list of all devices that had the software installed, then remoted into each and removed the software.”
Also whenever a software reaches EOL, such as an old version of Microsoft Office, the City of Vidalia uses Ninja to create a list of all devices that have the unsupported software installed, then decide whether to upgrade the software, find an open source replacement, identify if the software is still even used, or if it’s worth the risk of using the unsupported software.
The City of Vidalia also uses Webroot through Ninja for antivirus protection. “While we have firewalls for employees who are in the office and on the network, we’ve rolled out Webroot’s DNS content filtering to protect remote employees.” Over the past year, as employees have had to leave the office or quarantine, they’ve also leveraged Ninja’s end-user sharing feature. “We don’t need to open up the network or provide a VPN for employees who need to access on-network resources from home. We set them up as end-users in Ninja and they can access their resources from anywhere, without compromising network security,” says Andrew.
The City also has some endpoints with sensitive data access. Andrew has setup monitoring conditions on those endpoints, as needed, and is alerted to removable data devices being plugged into them. “When we get an alert that removable media has been used on those devices, we can notify their management who decide if it was used appropriately or not. We know which device was accessed, by which user, and what type of device was plugged in.”
The Ninja difference
“As someone who has worked with an RMM software package in the past,” says Andrew, “two things really stand out: Ninja’s ease-of-use and Ninja’s support. I love how easy it is to learn Ninja, and I love being able to pick up my phone and talk to a person.”
While Andrew had experience with a remote monitoring and management solution, the other technicians at City of Vidalia did not. “Within a couple of days, everyone on the team had a clear understanding of Ninja. We didn’t need training and there was no drawn out implementation process. We purchased Ninja and got started managing our infrastructure immediately. We started deploying to all of our departments while still in our 30-day trial, as we had already decided we were moving forward with Ninja.” explains Andrew.
With solutions Andrew had previously used, support was purchased separately from the product. Every support call was routed through an automated phone system to a centralized support team and each touch was charged against purchased support hours. “Ninja’s support is really amazing. I can call or email our account manager at any time. If there is an issue in Ninja or Webroot, she’s super reliable getting us to the right person to support us,” says Andrew.
Andrew finishes, “We’re a small team managing many different departments across our city. Each of those departments has its own location. With Ninja, the three of us are able to manage the IT needs of the entire city centrally and remotely so they can keep our city running and safe.”