Within every IT infrastructure, there are numerous entryways that cybercriminals leverage to steal data and harm businesses. One popular entryway is unpatched software. Almost every IT team out there dreads patching software, and it’s easy to see why. Patching is tedious and time-consuming work, and sometimes it disrupts systems so much that it does more harm than good. However, despite how frustrating patching endpoints can be, it’s critical for IT security. Read on, and we will reveal just how dangerous the consequences of unpatched software can be for IT teams.
What is unpatched software?
Unpatched software refers to applications or systems that contain known vulnerabilities that have not yet been addressed through the implementation of updates or patches. These vulnerabilities, if exploited, can potentially lead to a compromise of the affected system’s security.
As soon as these vulnerabilities are discovered and acknowledged by software vendors, patches are developed as a means of mitigating the identified risks. It is crucial to keep systems updated and patched using a clear patch management strategy. Failure to do so can leave systems exposed to potential exploits, as the threat actors are often aware of the vulnerabilities before patches are released.
Consequences of unpatched software in 2023
Leaving software unpatched and vulnerable creates some serious security weaknesses. Just take a look at a few of the data breaches that have occurred in 2023 within some of the largest and most well-known companies.
Data breaches of 2023
Reddit data breach
On June 19th of 2023, Reddit was targeted by the BlackCat ransomware gang; the organization threatened to release 80GB of confidential data that they had stolen from servers earlier in the year. BlackCat demanded $4.5 million as payment and wanted Reddit to revoke its new pricing policy.
T-Mobile data breach
Even though T-Mobile claims to have spent $150 million strengthening IT security in 2022, another attack has occurred this year. Unfortunately, T-Mobile is no stranger to cyberattacks, and the business has suffered once again from a widespread data breach on January 19th, 2023. The attack allowed cybercriminals to access the data of 37 million of T-Mobile’s prepaid and postpaid customers. Last year in 2022 when T-Mobile was attacked, cybercriminals compromised the data of 76 million customers.
MSI data breach
Micro-Star International (MSI), a popular computer vendor, was attacked by Money Message on April 6th, 2023. The ransomware organization claimed to have stolen 1.5TB of data and demanded $4 million as payment. If MSI refused to pay, the organization threatened to release the data they had accessed from the company’s systems to the public.
Check out this general list of consequences that unpatched software can have on your organization.
- Security vulnerabilities: One of the most significant consequences of unpatched software is an increased risk of security vulnerabilities. When software is not up to date with the latest patches, it may contain known security vulnerabilities that can be exploited by hackers or other malicious actors.
- Compliance issues: Many organizations are subject to regulations that require them to maintain secure systems and software. If your software is not up to date with the latest patches, you may be in violation of these regulations, which can result in fines, penalties, and other sanctions.
- Loss of data: Unpatched software can also result in the loss of sensitive data. If a security vulnerability is exploited, hackers may be able to access and steal confidential information, such as customer data or financial records.
- Damage to reputation: In today’s digital age, data breaches and other security incidents can have a major impact on an organization’s reputation. If your organization is affected by a security incident due to unpatched software, it could damage your reputation and make it difficult to regain customers’ trust.
- Lost productivity: In addition to the potential financial and reputational costs, unpatched software can also lead to lost productivity. If a security vulnerability is exploited and your systems are compromised, it can disrupt your operations and prevent your employees from working effectively.
Overall, the consequences of unpatched software can be severe and far-reaching. It’s important to implement patch management to ensure that your systems and software are always up-to-date and secure.
Cybersecurity & vulnerability statistics
The statistics listed below are only the most colorful recent examples of negligent patching practices, but many executives have their heads in the sand about the severity of the problem. “Small business owners tend not to focus on security because they see it as a liability and a cost center,” says AJ Singh, vice-president of product at NinjaOne. “They don’t consider the losses from outages.”
Let’s take a look at some of the top cybersecurity statistics of 2022 and 2023 to see just how important patching is for every IT team and business:
Malware and ransomware statistics
NinjaOne’s cybersecurity statistics report shows that:
- “The percentage of organizations victimized by ransomware attacks continues to grow yearly, reaching 71% of organizations in 2022.
- If 2023 keeps pace for ransomware payments, it’s projected to hit $898.6 million. This would make 2023 the second-biggest year for ransomware revenue, behind 2021, which estimates $939.9 million from ransomware victims.
- Only 57% of ransomware attacks have been successfully mitigated by restoring backups.”
Endpoint management and patching cybersecurity statistics
NinjaOne’s cybersecurity statistics report also emphasizes that:
- “70% of office workers use work devices for personal tasks
- 37% of office workers use their personal computers to access work applications
- 57% of data breaches could have been prevented by installing an available patch”
Unpatched vulnerabilities statistics
Automox’s 2022 unpatched vulnerability report shows these results:
- Unpatched vulnerabilities are directly responsible for 60% of all data breaches.
- Despite this statistic and the risks that unpatched software creates, this research shows that “A staggering majority of CIOs and CISOs even say that they delay putting security patches through to avoid interrupting business growth – and 25 percent say that they are certain their organization is not compliant with data security legislation.”
Post-pandemic cyber attack statistics
UpCity’s 2022 cybersecurity survey has a plethora of cybersecurity statistics:
- 43% of businesses feel financially prepared to take on a cyberattack
- 2021 cyberattacks cost U.S. businesses more than 6.9 billion dollars. Also, UpCity reveals that businesses are slowly adapting to post-pandemic security measures.
- “42% of respondents have revised their cybersecurity plan since the COVID-19 pandemic.”
High-Risk Behavior: Notable examples of unpatched software
Since 2023 is still in progress, who knows how many more cyberattacks will occur before the end of the year. Although 2023 has already had some serious attacks, they are minimal compared to the terrifying data breaches of 2022, as you’ll see below.
Unpatched software horror story |
# of records exposed |
Terrifying plot twist |
| Uber, one of the most popular transportation services, covered up an enormous data breach from a cybersecurity attack that affected both drivers and passengers who use the service. | 57 million | This data breach actually occurred back in 2016, but it was concealed until July 2022. Uber paid $100,000 to the hackers to prevent the event from going public. |
| Singtel is one of Asia’s top communications businesses, and a cyberattack revealed data from its businesses and customers. Although this cyberattack occurred two years ago, it was revealed publicly on October 10th, 2022. | 129,000 customers and 23 businesses | This breach revealed sensitive personal information of customers, such as names, birth dates, mobile numbers, addresses, and identity information. |
| Crypto.com is a currency exchange company, that allows users to convert their currency into cryptocurrencies such as Bitcoin and Ethereum. | 18 million in Bitcoin and 15 million in Ethereum | 483 accounts lost their funds due to a cyberattack and were able to access users’ virtual wallets. |
| The global social media platform Twitter suffered from a data breach in July of 2022. In August, the company confirmed publicly that the data breach had occurred and leaked users’ personal information. | 5.4 million | This data breach leaked the personal information, such as phone numbers and email addresses, of 5.4 million users. This was all due to a single vulnerability in the system that occurred after updating the code in 2021. |
How automated patching reduces security risks
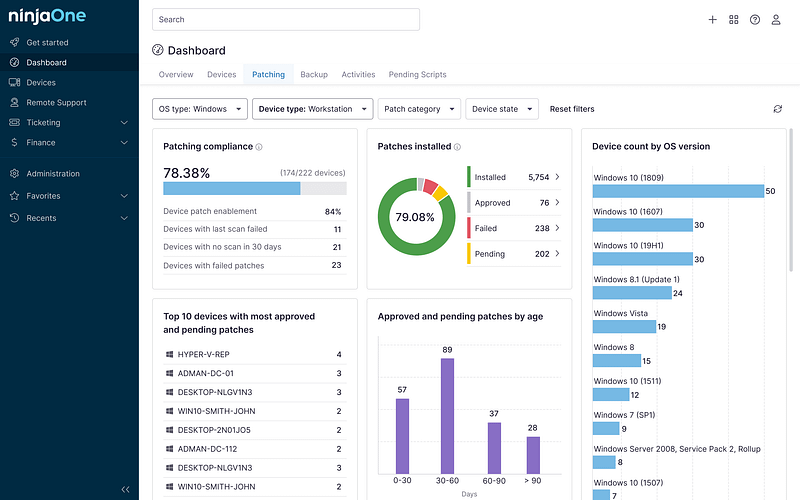
Though reputable vendors typically offer free, automated patching for outdated software, the process can sometimes break down or cause software to malfunction. “Patching is an uphill battle,” Singh says. “There are new threats out every day.” Our internal research at NinjaOne shows that 25-30% of Windows 10 patches fail, which is why we custom-built a utility to successfully execute the process and remediate threats.
Benefits of automated patching for IT teams
Automated patching is an indispensable tool for contemporary IT teams, offering a host of benefits that streamline and fortify operations. Firstly, it significantly reduces the manual workload, ensuring that software updates and vulnerability patches are consistently applied without the need for continuous oversight. This efficiency not only minimizes human error but also frees up IT professionals to focus on more strategic tasks and projects. Secondly, with cyber threats becoming increasingly sophisticated, automated patching ensures that systems are promptly updated, thereby reducing potential security breaches and safeguarding critical data. Furthermore, the “set it and forget it” nature of automated patching allows for uniformity in updates, ensuring all devices in a network are synchronized and compatible, reducing potential system conflicts or incompatibilities.
This level of consistency also enhances system performance and reduces downtime, leading to increased productivity. Additionally, the capability to tailor patching at a granular level gives IT teams the flexibility to adapt to specific organizational needs, allowing for custom patch schedules or selective patch deployments. In essence, automated patching provides IT teams with a combination of efficiency, security and flexibility, making it a cornerstone of effective IT management.
Discover how GSDSolutions was able to save time through automation.
“From a functionality perspective, patch management is really easy to setup and automate – and it really just works. Ninja’s integrations are fast and reliable. ”
Mark Andres, Director of IT Services at GSDSolutions
How to implement patch management
Before implementing patch management, ensure you have gone through these initial steps in your organization.
- Assessing needs: Before implementing patch management, it’s important to assess your organization’s needs. This will help you to determine the systems and software that need to be patched, as well as the frequency and scope of the patching process.
- Choosing a solution: There are many patch management solutions available, including both commercial and open-source options. When choosing a solution, consider factors such as ease of use, compatibility with your existing systems, and the level of support provided.
- Getting the right people involved: Patch management is not a one-person job. It’s important to involve the right people in the process, including IT staff, system administrators, and other relevant stakeholders. Training may also be necessary to ensure that everyone involved knows how to use the patch management solution and implement patches correctly.
- Creating a policy: Patch management should be a long-term process, not just a one-time event. To ensure that patches are implemented consistently and effectively, it’s important to create a patch management policy that outlines the processes, procedures, and responsibilities involved. This policy should be reviewed and updated regularly to reflect changes in your organization’s systems and software.
To implement patch management, follow these steps:
- Identify the systems and software that need to be patched. This can include operating systems, applications, and other types of software.
- Create a patch management schedule. Decide how often you will check for new patches and how you will implement them. For example, you may choose to check for new patches once a week and implement them on a monthly basis.
- Set up a patch management process. Determine who will be responsible for implementing patches and how they will be implemented. For example, you may decide to use a patch management tool to automate the process.
- Monitor the patch management process. Regularly check to make sure that patches are being implemented correctly and on schedule.
- Test patches before implementing them. It’s important to test patches in a non-production environment to make sure they don’t cause any issues before implementing them in your live systems.
- Keep track of all patches that have been implemented. This will help you to keep track of which systems and software are up to date and which may need to be patched in the future.
By following these steps, you can ensure that your systems and software are always up-to-date and secure. However, some additional aspects to consider when implementing patch management in your organization are as follows:
Eliminate security threats with NinjaOne patching
Ultimately, patching is both too important and too tedious for non-professionals to manage. That’s why NinjaOne offers patch management software that takes the pain out of this essential process. See why G2 ranked NinjaOne the #1 Patch Management Software in their latest report.